One-time pads are the holy grail of cryptography–they are impossible to crack, even in principle.
They work by adding a set of random digits to a message thereby creating a ciphertext that looks random to any eavesdropper. The receiver decodes the message by taking away the same set of random digits to reveal the original message.
The security of this process depends on two factors. The first is the randomness of the digits that make up the one time pad. If this key is truly random, it offers nothing the eavesdropper can use to break the code. Although there are some potential pitfalls, random digits are reasonably straightforward to generate these days.
The second factor is the ability to keep this key secret so that only the transmitter and receiver have access to it. That’s much more difficult to ensure.
Arxiv – Physical key-protected one-time pad
We describe an encrypted communication principle that can form a perfectly secure link between two parties without electronically saving either of their keys. Instead, cryptographic key bits are kept safe within the unique mesoscopic randomness of two volumetric scattering materials. We demonstrate how a shared set of patterned optical probes can generate 10 gigabits of statistically verified randomness between a pair of unique 2 cubic millimeter scattering objects. This shared randomness is used to facilitate information-theoretically secure communication following a modified one-time pad protocol. Benefits of volumetric physical storage over electronic memory include the inability to probe, duplicate or selectively reset any random bits without fundamentally altering the entire key space. Beyond the demonstrated communication scheme, our ability to securely couple the randomness contained within two unique physical objects may help strengthen the hardware for a large class of cryptographic protocols, which is currently a critically weak link in the security pipeline of our increasingly mobile communication culture.
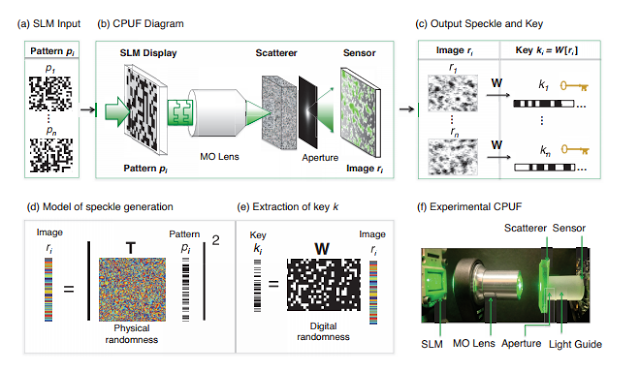
The construction and operation of a CPUF (communication physical unclonable function). (a) Sequentially over time, n random phase patterns pi are displayed on an SLM. (b) A microscope objective (MO) focuses each random wavefront from the SLM onto a volumetric scatterer. The scrambled light emerging from the material passes through a designed aperture before being detected by a CMOS sensor. (c) Each detected speckle image r is digitally transformed into an ideally random key k with a constant digital whitening projection operator W. (d) Optical scattering is mathematically represented by a complex random Gaussian matrix T and (e) digital whitening is described by a sparse binary random matrix W. The combination of one unique T and general W per CPUF device leads to an ideally random multi-gigabit key space that is very difficult to characterize or clone. (f) The experimental CPUF setup, including all components in (b).
Instead of creating and storing the one-time pad as a random sequence of 0s and 1s, Horstmeyer and co generate a random signal by passing light through a slab of diffusing glass that scatters it randomly.
The security of the system depends on the physical complexity of the glass. Horstmeyer and co say that that this complexity means there is no way for an eavesdropper, Eve, to copy the glass without anyone noticing.
That cuts out the need to store the key electronically and entirely removes this vulnerability to copying. “We describe an encrypted communication principle that can form a perfectly secure link between two parties without electronically saving either of their keys,” they say
And even if Eve steals the glass, they estimate that it would take her at least 24-hours to extract any relevant information about its structure.
This extraction can only be done by passing light through the glass at a rate that is limited by the amount of heat this creates (since any heating changes the microstructure of the material). And the time this takes should give the owners enough time to realise what has happened and take the necessary mitigating actions.
The CPUF devices used in experiment each contain a 2 megapixel transmissive phase SLM imaged onto opal diffusing glass, serving as our highly random scatterer. A 2 cm light guide (to increase the average detected speckle size) connects the scatterer to a 4.9 megapixel CMOS detector. During public dictionary setup, we display n = 5,000 different random phase patterns p to generate 174.4 gigabits of raw speckle data from two CPUFs, which is reduced to N = 10 gigabits of statistically verified randomness via the sparse matrix operator W. The approximate theoretical limit of 150 gigabits of randomness per CPUF link (derived in Supplement A) may be achieved using a thicker volumetric scatterer, currently limited to 0.5 mm for optical stability purposes. Improved-resolution SLM and CMOS arrays may allow random bit densities to eventually reach 1 terabit/mm3
Compared with a large, electronically saved one-time pad, the CPUF’s key is extremely challenging to copy or model and can easily scale to provide terabits of repeatable randomness within a small volume. Embedding the device’s digital electronics within its volumetric scattering material will further impede any attempted copy or probe attack. With additional study, we hope the convenient properties of optical scattering can solve enough of the OTP’s practical shortcomings to rejuvenate interest in its unbreakable security, even in the presence of infinite computing resources.
If you liked this article, please give it a quick review on ycombinator or StumbleUpon. Thanks

Brian Wang is a Futurist Thought Leader and a popular Science blogger with 1 million readers per month. His blog Nextbigfuture.com is ranked #1 Science News Blog. It covers many disruptive technology and trends including Space, Robotics, Artificial Intelligence, Medicine, Anti-aging Biotechnology, and Nanotechnology.
Known for identifying cutting edge technologies, he is currently a Co-Founder of a startup and fundraiser for high potential early-stage companies. He is the Head of Research for Allocations for deep technology investments and an Angel Investor at Space Angels.
A frequent speaker at corporations, he has been a TEDx speaker, a Singularity University speaker and guest at numerous interviews for radio and podcasts. He is open to public speaking and advising engagements.