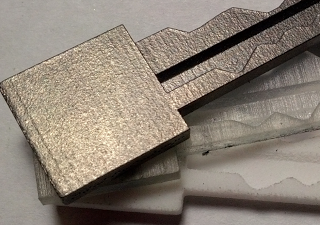
At the Def Con hacker conference Saturday, MIT students David Lawrence and Eric Van Albert plan to release a piece of code that will allow anyone to create a 3D-printable software model of any Schlage Primus key, despite the company’s attempts to prevent the duplication of those carefully-controlled shapes. With just a flatbed scanner and their software tool, they were able to produce precise models that they uploaded to the 3D-printing services Shapeways and i.Materialise, who mailed them working copies of the keys in materials ranging from nylon to titanium.
Schlage’s Primus models are advertised for use in high-security applications: The company’s marketing materials include references to the locks’ use in government facilities, healthcare settings, and detention centers. That security stems in part from Primus’s unique model, which includes two tracks of teeth–one on the top of the key and another on the side, each of which correspond to a separate set of pins in the lock. Even Marc Weber Tobias, one of the world’s most well-known lockpicking experts, has written that he uses Primus locks in his home and for secure evidence storage in his legal practice.
Lawrence’s and Van Albert’s software tool, to be clear, doesn’t let its users open any random door secured by one of those locks. It merely enables anyone to copy a key they couldn’t easily copy before. But the two students in MIT’s electrical engineering program point out that there are ways to copy a key without ever possessing it. Other researchers like those behind the Sneakey project have shown that keys can be effectively replicated from photos, even ones taken from hundreds of feet away.
And by studying Schlage’s manuals and patents, Lawrence and Van Albert learned to decipher the two distinct codes in the keys–one set of six numbers cut into the top of the key and another set of five in its sidecut–that can be programmed into their modeling software and precisely reproduced.
“All you need is a friend that works there, or to take a picture of their key, or even a picture of the key hanging off their belt,” says Lawrence. “Pirating keys is becoming like pirating movies. Someone still has to get the information in the first place, but then everyone can get a copy.”
The MIT students, who say they didn’t try printing the keys themselves on home 3D printers, used Shapeways to print working keys in nylon for less than $5 each, though a more durable titanium copy from i.Materialise.com cost them $150.
Separately – Digital Hacking to Hijack moving cars
omebody commandeers control of your car with you in it.
That was the scary scenario painted over the first two hours at the 21st annual Defcon hacker conference.
“Car hacking is definitely coming,” said Zoz, of Cannytophic Design, who presented on how to hack autonomous cars.
Zoz’s talk on vulnerabilities that autonomous autos will face followed a fast-paced explanation by well-known computer security experts Charlie Miller and Christopher Valasek of how they spent the past 10 months hacking the self-driving features of two popular cars.
SOURCE – Forbes, CNET, Youtube, Fabbaloo
If you liked this article, please give it a quick review on ycombinator or StumbleUpon. Thanks

Brian Wang is a Futurist Thought Leader and a popular Science blogger with 1 million readers per month. His blog Nextbigfuture.com is ranked #1 Science News Blog. It covers many disruptive technology and trends including Space, Robotics, Artificial Intelligence, Medicine, Anti-aging Biotechnology, and Nanotechnology.
Known for identifying cutting edge technologies, he is currently a Co-Founder of a startup and fundraiser for high potential early-stage companies. He is the Head of Research for Allocations for deep technology investments and an Angel Investor at Space Angels.
A frequent speaker at corporations, he has been a TEDx speaker, a Singularity University speaker and guest at numerous interviews for radio and podcasts. He is open to public speaking and advising engagements.